Role Based Authentication In ASP.NET MVC
What is Role Based Authentication In ASP.NET MVC?
Role Based Authentication is Membership and Role providers. These providers allows us to define Roles, Users and assign roles to users which helps us to manage Authorization. But with an increase in social networking and global authentication providers, we needed an upgraded membership system. ASP.NET Identity is the new membership system for building ASP.NET web applications, phone, store, or hybrid applications using social identities for authentication and authorization. So we can now use Windows Live (e.g. Hotmail), Gmail, Facebook and Twitter for authentication before the user starts using our web application.
Adding role checks
Role-based authorization checks are declarative—the developer embeds them within their code, against a controller or an action within a controller, specifying roles which the current user must be a member of to access the requested resource.
For example, the following code limits access to any actions on the AdministrationController to
users who are a member of the Administrator role:
- [Authorize(Roles = “Administrator”)]
- public class AdministrationController : Controller
- {
- }
For multiple roles as a comma separated list
- [Authorize(Roles =”Admin,Employee”)]
- public ActionResult Index()
- {
- var employees = db.Employees.Include(e => e.Department);
- return View(employees.ToList());
- }
If you apply multiple attributes then an accessing user must be a member of all the roles
specified; the following sample requires that a user must be a member of both the PowerUser
and ControlPanelUser role.
- [Authorize(Roles = “PowerUser”)]
- [Authorize(Roles = “ControlPanelUser”)]
- public class ControlPanelController : Controller
- {
- }
In the project add a new folder called CustomFilters and add the class file with following login logic
in it:
- using System.Web.Mvc;
- namespace A11_RBS.CustomFilters
- {
- public class AuthLogAttribute : AuthorizeAttribute
- {
- public AuthLogAttribute()
- {
- View = “AuthorizeFailed”;
- }
- public string View { get; set; }
- /// <summary>
- /// Check for Authorization
- /// </summary>
- /// <param name=”filterContext”></param>
- public override void OnAuthorization(AuthorizationContext filterContext)
- {
- base.OnAuthorization(filterContext);
- IsUserAuthorized(filterContext);
- }
- /// <summary>
- /// Method to check if the user is Authorized or not
- /// if yes continue to perform the action else redirect to error page
- /// </summary>
- /// <param name=”filterContext”></param>
- private void IsUserAuthorized(AuthorizationContext filterContext)
- {
- // If the Result returns null then the user is Authorized
- if (filterContext.Result == null)
- return;
- //If the user is Un-Authorized then Navigate to Auth Failed View
- if (filterContext.HttpContext.User.Identity.IsAuthenticated)
- {
- // var result = new ViewResult { ViewName = View };
- var vr = new ViewResult();
- vr.ViewName = View;
- ViewDataDictionary dict = new ViewDataDictionary();
- dict.Add(“Message”, “Sorry you are not Authorized to Perform this Action”);
- vr.ViewData = dict;
- var result = vr;
- filterContext.Result = result;
- }
- }
- }
- }
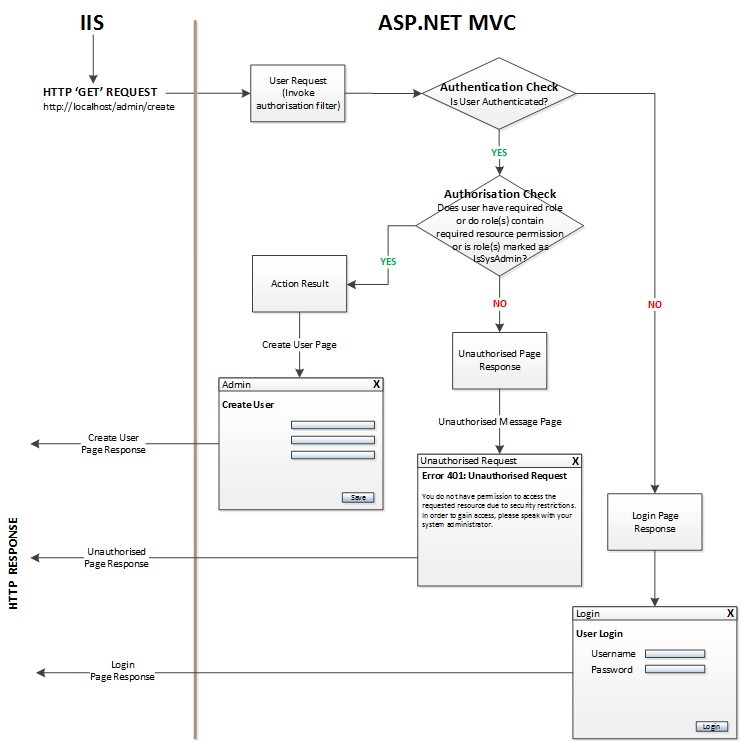
custom filter is derived from AuthorizeAttribute class and overrides the OnAuthorization() method. The IsUserAuthorized() helper method checks the user authentication with AuthorizationContext class. If the Result property returns null, then the
Authorization is successful and user can continue the operation; else if the user is authenticated but not authorized, then an Error Page will be returned.
If you’re using MVC 5 you have to enable lazy loading in your DbContext by putting the
following line in your DbContext initialisation.
this.Configuration.LazyLoadingEnabled = true;
Author – Disha Raval